
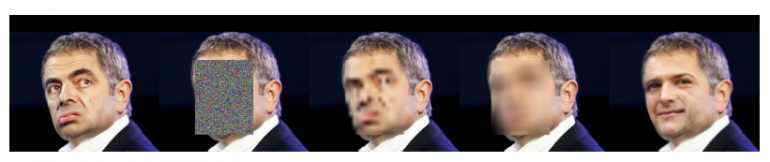
A group of researchers from the Norwegian University of Science and Technology has proposed a method for automatic face anonymization by superimposing a generated face on the input image.
The method called Deep Privacy leverages the power of a generative adversarial neural network that generates a face taking into consideration the person’s pose, position and image background. According to the researchers, the background information together with the generative power of GAN networks enables them to generate realistic faces that fit the person and the background in the image.

They designed and input scheme that allows the network to learn this seamless transition between a generated face image and the present conditional information as the background. Their method is based on a few simple annotations of the image that needs to be anonymized and a Generative Adversarial Network.
The input image is first annotated with a bounding box representing a person’s face and several facial keypoints that should lead the learning towards seamless pose estimation. The input to the network is again an image with a masked out region within the bounding box and filled with random noise, together with the keypoints detected.
Researchers propose a generator model which follows an encoder-decoder architecture and combines the layer’s output with the pose information in the decoder. They also introduced a novel and diverse dataset of human faces with unconventional poses and occluded faces, needed for training of their proposed model.
Experiments were conducted using the WIDER Face dataset and researchers compared the proposed method with several different anonymization methods. They showed that the method achieves better results than existing anonymization methods while retaining a realistic image. Several ablation experiments were also designed by them, using the novel dataset that researchers proposed.
The implementation of the Deep Privacy method was open-sourced and it’s available on Github. The paper explaining the method in more detail can be found on arxiv.
[…] Source: DeepPrivacy: GAN Network Anonymizes Images Using Generated Faces […]